Introduction
If you are working with Palo Alto firewalls and Panorama, you've probably experienced a number of issues.
Maybe you have been working with them long enough to see a decrease in stability and an increase in the number of bugs and new errors.
That's my observation, at least. I started working with PA firewalls when the 7.x release train was the standard and 8.x was just around the corner.
9.x was a very decent release, but since 10.x, it's just been a downward spiral of slowness, instability, and bugs.
But PA is promising improvements starting with 12.1 (surprisingly, this time .0 was skipped by PA).
However, as of today, we are still waiting for a recommended version, meaning there is no stable version in the 12.x release train yet.
Anyway, I wanted to give it a shot and build my lab on 12.1.4-h3 to check how much it differs from 11.2.x and if there are any actual improvements.
Kickoff
So here we are: my lab FW running 11.1.x and a freshly installed Panorama on 12.1. Everything is in place:
- Connectivity between the FW and Panorama
- Ports opened
- Visible sessions in session browser towards Panorama
- DeviceCert on both the FW and Panorama
- No typos in the FW serial number in Panorama
- Time synchronized
- Panorama on a higher software version than the FW
...but the FW is still "disco" (dancing! 😄).
Since we already did a basic troubleshoot and ensured that all of the above is in place, it's time to take out the big guns.
Logs, logs, logs
In those situations, logs are your best friend, but you need to know exactly where to look and what to look for.
tail follow yes lines 50 mp-log ms.log
2026-02-23 21:46:45.152 +0100 update client device info, n_entries=1 op=1
2026-02-23 21:46:45.152 +0100 Device info updated for client id 1005371 device_registered yes
2026-02-23 21:46:53.822 +0100 Error: sni_ssl_servername_cb(src_cms/cms_server.c:664): Unknown SNI: 'xxx-ceab-408d-ade5-xxx'. 40A63E2EE17F0000:error:0A0000EA:SSL routines:final_server_name:callback failed:ssl/statem/extensions.c:1014:Alright, it looks like there's an issue with the handshake/certificate. Let's dig deeper.
tail lines 500 mp-log configd.logAnd there, buried somewhere in all the noise, I found my FW_SERIAL_NO:
2026-02-23 21:46:45.111 +0100 Processing lcs-register message from device 'FW_SERIAL_NO'
2026-02-23 21:46:45.111 +0100 processing a register message from FW_SERIAL_NO. sock=-1
2026-02-23 21:46:45.111 +0100 SC3: did:'FW_SERIAL_NO', ser:'(null)', ver:'11.1.6-h10', mod:'(null)'
2026-02-23 21:46:45.111 +0100 Error: sc3_register(sc3_register.c:192): SC3: register - incomplete register info
2026-02-23 21:46:45.111 +0100 Error: pan_cfg_handle_mgt_lcsreg(pan_cfg_mgt_handler.c:3196): SC3L: Failed to register device: 'FW_SERIAL_NO'. Ignored.Gotcha! It looks like there is an issue with the SC3 register, which is why my firewall isn't able to connect to Panorama.
Fortunately, PA has prepared a KB article around SC3 register issues, so let's follow the steps.
Fixing the issue
Alright, it seems it's just a couple of steps...
rogala@pa-fw> request sc3 reset
WARNING: executing this command will reset SC3 state on this device. You will need to re-onboard the system (using an authkey). Do you want to continue? (y or n)
SC3 has been reset!
You need to restart mgmtsrvr to reinit SC3.
rogala@pa-fw> debug software restart process management-serverAfter that operation we can see different logs on Panorama now:
2026-02-23 22:35:34.849 +0100 Warning: _register_ext_validation(pan_cfg_mgt_handler.c:4769): reg: device 'FW_SERIAL_NO' not using issued cert.
2026-02-23 22:35:34.849 +0100 SC3: did:'FW_SERIAL_NO', ser:'FW_SERIAL_NO', ver:'11.1.6-h10', mod:'PA-440'
2026-02-23 22:35:34.850 +0100 Warning: sc3_register(sc3_register.c:213): SC3: connstat for 'FW_SERIAL_NO': -1
2026-02-23 22:35:34.850 +0100 Warning: sc3_register(sc3_register.c:250): SC3: register device 'FW_SERIAL_NO' does not have a peer cert.
2026-02-23 22:35:34.850 +0100 Error: sc3_register(sc3_register.c:271): SC3: register - No authkey given for device 'FW_SERIAL_NO'
2026-02-23 22:35:34.850 +0100 Error: pan_cfg_handle_mgt_reg(pan_cfg_mgt_handler.c:5122): SC3: Failed to register device: 'FW_SERIAL_NO'And now I got this nice warm feeling that it's closer to solution now.
Let's get back to FW and finish the procedure:
rogala@pa-fw> request authkey set 2:-this-is-very-long-and-complicated-auth-key-
Authkey set.
rogala@pa-fw> configure
Entering configuration mode
[edit]
rogala@pa-fw# commit force
Commit job 60288 is in progress. Use Ctrl+C to return to command prompt
.................................55%.....98%....................................100%
Performing panorama connectivity check (attempt 1 of 5)
Panorama connectivity check was successful for 10.0.200.200
Configuration committed successfullyDo you see this? It's already visible during the commit, we do have Panorama connectivity!
Let's go back to Panorama logs again:
2026-02-23 22:37:54.884 +0100 Warning: _register_ext_validation(pan_cfg_mgt_handler.c:4769): reg: device 'FW_SERIAL_NO' not using issued cert.
2026-02-23 22:37:54.884 +0100 SC3: did:'FW_SERIAL_NO', ser:'FW_SERIAL_NO', ver:'11.1.6-h10', mod:'PA-440'
2026-02-23 22:37:54.884 +0100 Warning: sc3_register(sc3_register.c:213): SC3: connstat for 'FW_SERIAL_NO': -1
2026-02-23 22:37:54.884 +0100 Warning: sc3_register(sc3_register.c:250): SC3: register device 'FW_SERIAL_NO' does not have a peer cert.
2026-02-23 22:37:54.991 +0100 sc3_sign_csr_scripter: invoked
2026-02-23 22:37:55.093 +0100 connmgr: received disconnect cb from ms for FW_SERIAL_NO-log-collection-lr-cms0-def(1005821)
2026-02-23 22:37:55.093 +0100 connmgr: connection entry removed. devid=FW_SERIAL_NO-log-collection-lr-cms0-def sock=4294967295 result=0
2026-02-23 22:37:55.094 +0100 Handling device conn update [disconnection][activated:1] for FW_SERIAL_NO-log-collection-lr-cms0-def: "server: client is lc or device-lc"
2026-02-23 22:37:55.095 +0100 Device lcs agent FW_SERIAL_NO-log-collection-lr-cms0-def disconnected
2026-02-23 22:37:55.095 +0100 connmgr: connection entry removed. devid=FW_SERIAL_NO-log-collection-lr-cms0-def (1005821)
2026-02-23 22:37:55.111 +0100 mgmt-certs.sh script started successfully: { 'args': [ sign, -c, FW_SERIAL_NO, -s, ffffffff-83de-46e6-977c-02ff30fffe49, -t, fw, ], }
2026-02-23 22:37:55.111 +0100 sc3_sign_csr_scripter: finished ret 0
2026-02-23 22:37:55.111 +0100 Warning: sc3_register(sc3_register.c:359): SC3: Register - signed CSR for device: 'FW_SERIAL_NO'.
2026-02-23 22:37:55.111 +0100 SC3: Register - using key: 'default' for device: 'FW_SERIAL_NO'.
2026-02-23 22:37:55.111 +0100 Warning: pan_cfg_handle_mgt_reg(pan_cfg_mgt_handler.c:5103): SC3: Registering device 'FW_SERIAL_NO'
2026-02-23 22:37:55.113 +0100 SVM registration. Serial:FW_SERIAL_NO DG: TPL: vm-mode:0 uuid: cpuid: svm_id:2026-02-23 22:37:55.113 +0100 processing a register message from FW_SERIAL_NO
2026-02-23 22:37:55.114 +0100 pan_conn_set_conn_details: device_type:server: client is device
2026-02-23 22:37:55.114 +0100 received a reg message from FW_SERIAL_NO. Creating conn entry.
2026-02-23 22:37:55.139 +0100 Got HA state from device FW_SERIAL_NO, local state: unknown, peer state: unknown
2026-02-23 22:37:55.139 +0100 Error: parse_cluster_config_info(pan_cfg_mgt_handler.c:4071): Node FW_SERIAL_NO is missing cluster-info/nodetype!
2026-02-23 22:37:55.139 +0100 Error: parse_cluster_config_info(pan_cfg_mgt_handler.c:4083): Node FW_SERIAL_NO is missing cluster-info/hsci-c0-ip-address!
2026-02-23 22:37:55.139 +0100 Error: parse_cluster_config_info(pan_cfg_mgt_handler.c:4095): Node FW_SERIAL_NO is missing cluster-info/inter-firewall-qos-lo-ip!
2026-02-23 22:37:55.139 +0100 Error: parse_cluster_config_info(pan_cfg_mgt_handler.c:4107): Node FW_SERIAL_NO is missing cluster-info/inter-firewall-qos-medium-ip!
2026-02-23 22:37:55.139 +0100 Error: parse_cluster_config_info(pan_cfg_mgt_handler.c:4119): Node FW_SERIAL_NO is missing cluster-info/inter-firewall-qos-high-ip!
2026-02-23 22:37:55.139 +0100 Unable to find dg for FW_SERIAL_NO, vsys1
2026-02-23 22:37:55.143 +0100 License info missing in db for device FW_SERIAL_NO, refreshing
2026-02-23 22:37:55.143 +0100 No cookie available for this request
2026-02-23 22:37:55.144 +0100 Update licenses info job 17 scheduled
2026-02-23 22:37:55.146 +0100 first_full_commit is set to false for PA
2026-02-23 22:37:55.157 +0100 pan_conn_entry_add_base(cs_conn.c:1780): connmgr, channel registered 3.
2026-02-23 22:37:55.158 +0100 connmgr: connection entry added: devid=FW_SERIAL_NO (1005822)
2026-02-23 22:37:55.158 +0100 FW_SERIAL_NO is now connected
2026-02-23 22:37:55.168 +0100 Handling device conn update [new connection][activated:1] for FW_SERIAL_NO: "server: client is device"
2026-02-23 22:37:55.169 +0100 connection to FW_SERIAL_NO is now readyAnd finally in the GUI:
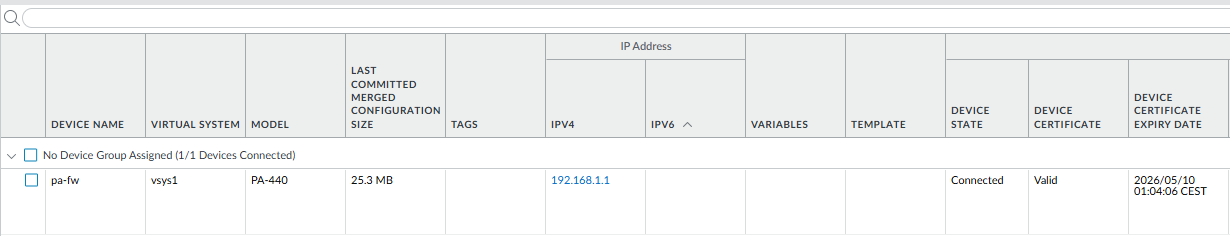
My FW is finally connected to Panorama! And I can move forward.
Conclusion
Since the PA 10.x release, I've learned one thing: if you're planning anything more than simple firewall policy management, expect the unexpected.
You can see from the timestamps in the logs how long it took me to fix the issue (of course, you have to add some extra time for me to grab results for the blog).
Anyway, what was supposed to be simple lab prep for another topic turned into an unplanned blog entry! 😊